Explainer: Why cyber threats and scams remain a challenge in South Sudan?
Misinformation and disinformation have been weaponised as tools to build trust and to create convincing narratives in phishing email messages or inbox alerts that influence users to accept or take action, whether by revealing their sensitive information.
Writer: Makur Majeng
As the digital space in South Sudan evolved, it has opened the door to cyber threats and scams from social media platforms and other online channels. The digital space continues to be the biggest driver of information dissemination among human populations, powered by both internet and mobile telecommunications penetration in the country.
Facebook and WhatsApp are widely used means of communication for a great majority. However, these platforms have become grounds for numerous cyber threats and scams—a real danger to users.
Cyber threats are malicious acts that seek to damage data, steal data, or disrupt digital systems. It is normally perpetrated by individuals, criminal organisations, state actors, and terrorist organisations to achieve specific objectives.
Social media scams are suspicious activities by individuals who create fake profiles or pages and unexpectedly contact users on social media to gain their trust and manipulate them. A social media scammer pretends to be a friend, family member, or anybody with specific interests.
On the other hand, they impersonate real business entities, employers, the government, and investment or online trading platforms.
This explainer provides an analysis to understand why such threats continue in South Sudan’s social media space.
Cyber Threats and Scams
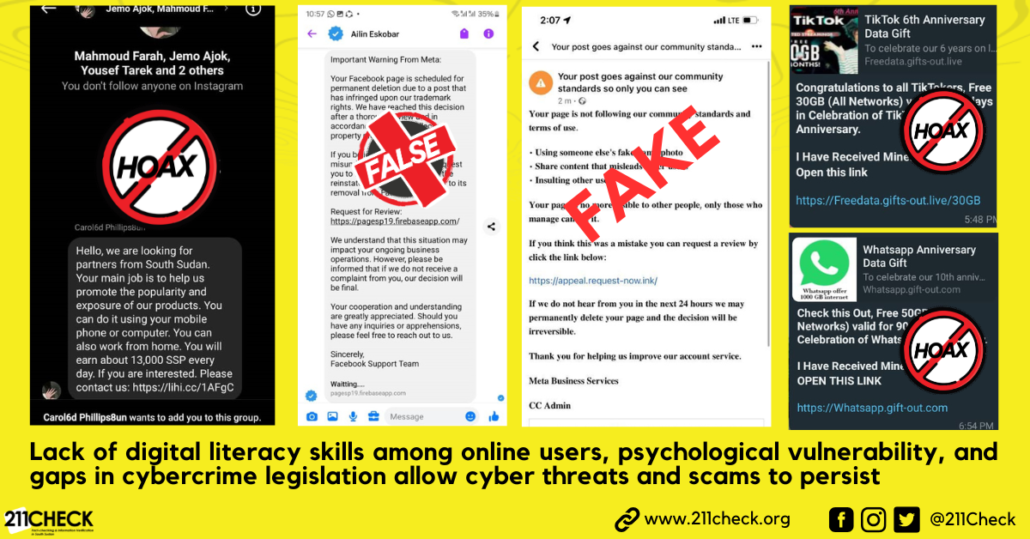
According to a joint advisory issued by SafetyComm and 211 Check, in September this year, there are different categories of cyber scams rampant in South Sudan.
There have been false alarms where users receive notification messages directly in their inbox or email claiming to be sent from Meta or Facebook about page verification, violations of community standards, and copyright infringement.
Some of these messages contain threats of account deletion or suspension and demand users to click malicious links within the next few hours. The intention is to entice the users to click malicious links that may lead to the compromise of their accounts.
In addition to that, a phishing attack has been used to acquire personal information such as usernames, passwords, and credit card details. The attack weaponised malicious links embedded into the false alarm notification messages by those masquerading as trustworthy individuals or entities.
These cyber threats and scam operations involve social engineering techniques by cybercriminals seeking to manipulate victims into providing their confidential data.
This method involves using lures to obtain clicks, masquerading as known entities or contacts to entice the victim into providing confidential data like passwords, and clicking on a malicious link embedded within job advertisements, promotions, fake giveaways, or investment schemes.
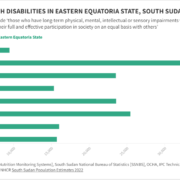
In the last five years, SafetyComm recorded a total of 854 compromised social media accounts between 2021 and 2024. Most of the cyber threats and scams take place on the Facebook platform, which amounts to 57.3%, with WhatsApp (22.8%) and Instagram (18.9%), as documented by the SafetyComm.
The dangers that come after being comprised is that confidential data not meant for the public will get its way into the hands of unauthorised persons, leading to identity theft, data loss, and, in the worst-case scenario, unauthorised access to private materials like nudes.
Common Cyber Scams
Scammers send messages with claims that a user’s profile has met the requirements for a verified badge from Meta, and then users are asked to click shady links within 24 hours before it expires. Users received false alerts that they had violated Meta’s Community Standards by allegedly using fake photos or distributing misleading content and directing users to request a review through a malicious link.
Also, scammers threaten users that their accounts have violated copyright infringement and will be deleted if users fail to repeal the incident through a dubious link.
So why are cyber scams still rampant in South Sudan?
Many social media users do not have the necessary basic cyber security knowledge and tools to detect and prevent deceptive messages or fraudulent activities. This makes them vulnerable to clicking on malicious email links without a second thought as to whom the link is coming from, as well as reacting to providing confidential personal data when asked by impersonators.
There are no strong mechanisms now to enforce cyber laws due to a lack of legal basis and expertise by law enforcement agencies in prosecuting various cyber fraud schemes. The Cybercrime and Computer Misuse Bill is still in parliament for deliberations. This shortcoming has empowered cybercriminals to perpetrate deadly operations against online users in the country.
The Role of Misinformation and Disinformation
Misinformation and disinformation have been weaponised as tools to build trust and to create convincing narratives in phishing email messages or inbox alerts that influence users to accept or take action, whether by revealing their sensitive information like passwords, credit card numbers, and personal details or by doing what the message has urged them to do.
In this context, by spreading false or misleading information, attackers and scammers exploit online users’ emotions in terms of fear and curiosity to lure them in by clicking on malicious links or providing confidential data.
Conclusion:
The digital landscape in South Sudan has significantly remained vulnerable to cyber threats and scams. This is due to a lack of strengthened information technology infrastructure and a lack of digital literacy skills among online users, which leaves them vulnerable to social engineering tactics employed by cybercriminals.
The absence of enforceable cyber laws has created an environment where perpetrators operate with relative impunity, exploiting loopholes and targeting unsuspecting users on platforms like Facebook and WhatsApp.
To overcome these threats, there is a need to improve cybersecurity infrastructure and enhance digital literacy to empower the public on how to detect and avoid cyber scams. Besides, the national parliament should fast-track the enactment of the Cybercrime and Computer Misuse law to set the stage for enforcement to protect online users.
To ensure accuracy and transparency, we at 211 Check welcome corrections from our readers. If you spot an error in this article, please request a correction using this form. Our team will review your request and make the necessary corrections immediately, if any.
It’s vital to fight misinformation and disinformation in the media by avoiding fake news. Don’t share content you’re uncertain about. False information can harm and mislead people, risking their lives—Fact-check before sharing. For more details, visit https://211check.org/, or message us on WhatsApp at +211 921 350 435. #FactsMatter.

 211 Check Website Graphics
211 Check Website Graphics
 211 Check Website Graphic Image Feature
211 Check Website Graphic Image Feature 

I caught my husband so many times through his chats and all about cheating on me and when i told him he always claims that he has changed and all. right now he hides his phone from me and i still guess he is cheating cause i could not break into his phone any more so i was referred to a hacker named FRED who i ran to for help and this hacker was able to break into his phone and proved me with the access to my husband phone without my spouse knowing about the hack. Right in my phone I have all my husband’s daily activities . I got to read all his chats, texts, calls, WhatsApp, Facebook, and many more. This hacker is really great, thank you. Did you find this review helpful? contact him via Gmail [email protected] and you can text,call him on +15177981808 or +19782951763
Wondering, how to track a cheating wife and obtain proof of her unfaithfulness? Well, the easiest way to catch a cheating wife is to access your spouse’s phone remotely without them ever finding out. With such a cyber professional ( spycheating partner @ G(m)Ail c0m) you can do a lot more than just read her text exchanges in real time. For instance, you can use Remote spy hacker to catch your wife cheating on WhatsApp or other messaging apps. Once you provide her phone number and they get her data activated, it allows you to remotely access all WhatsApp texts and photos, as well as messages from social media platforms like Facebook, Instagram, and Snapchat in real-time. It even offers GPS
i had similar issues trying to recover some lost files and they were very important . i tried many tools online , watched videos that will guide me through but all was a waste of time . i felt recovery can’t be possible but then i had this friend who introduced me to Vladmir who specializes on recovery . so i gave him a try and after giving him all necessary details. He actually helped me get back all the lost files. Like i didn’t believe it till i was convinced. so honestly it’s possible to recover any thing you’ve lost or can’t access. You just have to find someone in such field to help you. But if you want to try same person that helped me then you can through ; Remotespyhacker (AT) g(m)a1l dot c0m . Just helping out
Marriage is sweet, Love is also sweet but i don’t see why after getting married to my dream man he still cheated on me with his EX girlfriend though i had try breaking into his IPHONE since last year but still not getting access to his phone since then i just try to swallow all my husband had been doing but i can’t take it any more so i came in contact to gmail of jbeespyhack @gmail com, with his help I had access to my husband’s phone without touching his phone. I had full information of his chats with his ex-girlfriend last year. With all I saw, I don’t think I can move on with the marriage. He went as far as telling the girlfriend that I have been his wrong & i beat her up almost everyday. I was so disappointed & I called off the marriage.. and jbeespyhack@gmail com and you can text him your request
YOU GOT SCAMMED⁉️
HERE IS WHAT YOU NEED TO DO‼️
Contact “SEFTYHUB ” Immediately ✅✔️ using any of the emails below -:
SEFTYHUB @GMAIL COM
TELEGRAM @SEFTYHUB
Contacting Authorities might be helpful but most times this scam cases are not taking seriously especially if the money lost isn’t as much or people scammed aren’t as many. Most times people feel ashamed to contact authorities.
WHO OR WHAT IS SEFTYHUB ⁉️
SEFTYHUB are a group of skilled hackers who use their skills to help individuals who got scammed and defrauded by tracking down the scammers using information provided. The internet today is filled with fake adverts used to scam people of their money and there isn’t really anyway to stop it. The adverts promoting this scams are so convincing and realistic that you really can’t differentiate it from what is legit and what isn’t.
Some of the common scam that really takes a lot from people are things like-:
❌ Crypto & Forex Trading Scam
❌ Bank Loan Scam
❌ Buying & Purchasing Products Online
❌ Dating Scam (Catfishing)
❌ Black
HOW WILL SEFTYHUB HELP, YOU MIGHT ASK❓
We what SEFTYHUB basically do is use information you can provide about a scammer, to determine the best strategy to help you get your money back. Everything SEFTYHUB do is professional and won’t be traced back to you as they keep their work discreet and clean.
It doesn’t matter how much you were scammed, doesn’t matter what you were in contact with the scammers for, they will take up your case and will do everything within their disposal to get your money back.
If you happen to be a victim of scammers and you reading this now, take a deep breath and stay calm, you are getting your money back. You are just an email away.
Contact Email-:
SEFTYHUB @GMAIL COM
GLENDARSEFTYHUB @GMAILCOM
TELEGRAM @SEFTYHUB
SEFTYHUB
2023@
2026 02:34
2026 02:00 How Do I Recover My Stolen Crypto Without Being Scammed During The Recovery Process Again. | Safe Guide And Recovery With Intelligence Cyber Wizard? Cryptocurrency Theft: What Victims Need to Know and How to Respond. Cryptocurrency theft is one of the most devastating experiences for holders, traders, and investors. Unlike traditional bank fraud, where transactions can sometimes be reversed, cryptocurrency transactions are irreversible by design. While this ensures privacy and security, it also leaves victims with limited recovery options once funds are stolen. In this environment, Intelligence Cyber Wizard Recovery (Blockchain Dev) focuses on educating victims and guiding them through practical steps toward potential recovery. Why Cryptocurrency Theft Happens. Understanding how theft occurs is the first step toward prevention and response. Common causes include: Phishing scams: Fake websites or messages trick users into revealing private keys; Malware and keyloggers: Software designed to steal login credentials; Exchange hacks: Third-party platform breaches; Money theft and fraudulent projects: Deceptive schemes that disappear with investor funds; Human error: Lost seed phrases or sending funds to incorrect addresses. Once funds leave your wallet, reversing the transaction is extremely difficult. However, informed action can still make a difference. The role of cyber intelligence recovery: This is not a “magic bullet,” but a structured system of education and support designed to empower victims. The goal is to replace panic with informed and strategic action. 1. Education on the Post-Theft Reality: Victims are guided to understand: How blockchain transactions work; Why transactions cannot simply be reversed; What “traceability” means in blockchain systems; The limitations of law enforcement in different jurisdictions; Common scam patterns to avoid. This helps prevent costly, panic-driven mistakes. 2. Step-by-Step Recovery Guide: While full recovery is not guaranteed, there are practical steps: Trace stolen funds; Identify exchange endpoints; Detect the use of mixers or tumblers; Trace wallet-to-wallet movement patterns. Victims learn how to gather and organize evidence into useful intelligence; Inform forensic teams; Submit detailed investigation reports; Provide transaction identifiers, wallet addresses, and screenshots; Escalate cases through the appropriate channels. Proper reporting increases the chances of coordinated intervention. 3. Access to Experts: Victims can connect with: Blockchain forensic analysts, Cybersecurity professionals, Legal experts in digital asset crimes. This reduces confusion and ensures structured support. 4. Emotional and Community Support: Losing cryptocurrency can be emotionally overwhelming. Support includes: Peer-to-peer discussion groups, Secure forums for sharing experiences, Stress management guidance. Clear thinking is critical during recovery efforts. 5. Prevention Through Education: A key focus is helping victims avoid future losses: Secure storage of seed phrases, Understanding hardware wallets, Setting up two-factor authentication, Recognizing social engineering tactics, Realistic Expectations. It’s important to be honest: Full recovery is rare, but not impossible; Stolen funds can sometimes be traced; Exchanges can freeze assets if alerted quickly; Coordinated investigations can improve outcomes. The focus remains on realistic, data-driven actions, not false promises. Key takeaways for victims: Act quickly, time is critical. Document everything (transactions, messages, addresses). Avoid panicked decisions. Use blockchain tracking tools. Seek legal and expert guidance. Conclusion: Recovering stolen cryptocurrency is challenging, but not hopeless. With the right combination of knowledge, forensic tools, expert support, and legal guidance, victims can take important steps toward recovery and better protect themselves in the future. To initiate a review of your case, you can contact the forensic investigation team: Telegram: @SEFTYHUB EMAIL:SEFTYHUB @GMAIL COM Once your request is received, the team will respond with the next steps to evaluate your
REPLY
Wondering, how to track a cheating wife and obtain proof of her unfaithfulness? Well, the easiest way to catch a cheating wife is to access your spouse’s phone remotely without them ever finding out. With such a cyber professional ( REMOTE SPY HACKER @ G(M)AIL C0M ) you can do a lot more than just read her text exchanges in real time. For instance, you can use Remote spy hacker to catch your wife cheating on WhatsApp or other messaging apps. Once you provide her phone number and they get her data activated, it allows you to remotely access all WhatsApp texts and photos, as well as messages from social media platforms like Facebook, Instagram, and Snapchat in real-time. It even offers GPS tracking, allowing you to view their location on Google Maps.
I never thought I would fall victim to a crypto scam until I was convinced of a crypto investment scam that saw me lose all my entire assets worth $487,000 to a crypto investment manager who convinced me I could earn more from my investment. I thought it was all gone for good but I kept looking for ways to get back my stolen crypto assets and finally came across Ethical Hack Recovery, a crypto recovery/spying company that has been very successful in the recovery of crypto for many other victims of crypto scams and people who lost access to their crypto. I’m truly grateful for their help as I was able to recover my stolen crypto assets and get my life back together. I highly recommend their services
EMAIL ETHICALHACKERS009 AT @GMAIL DOT COM
whatsapp +14106350697
My marriage of 19 years is about to be broken after remotely reading my wife WhatsApp messages with her Boyfriend, that was when I knew I married a smart cheat because she has been seeing this guy 4 years now!!! And I didn’t suspect anything not until I hired ( Zattechhacker @ gmail com ) who gave me 100% access into my wife phone, and all of this was done remotely. Thank you once again ( Zattechhacker @ gmail com )
Hello, everyone, my name is Jessey Anthony am from the Australia-Queensland I was so happy to see a testimonial given by someone called Petrov Ganovish about his cheating ex-wife that wanted his father’s money so I have to contact the email of the man that helps him out in exposing her, for him to help me to expose my husband cheating and wrong deals with other women out there i had to contact PROFESSIONAL WIZARD HACKERS to assist me in the job right now, i have complete access to his phone. I got concrete evidence. it was unbelievable to see the evidence of my hubby cheating on me. Who likes to live with a cheater, I used the evidence I got to file for a divorce. I’m thankful to PROFESSIONAL WIZARD HACKERS for helping me out of my dilemma and suspicions. His services are highly rated and affordable he is best and good in his work contact him email: [email protected] or [email protected] / WhatsApp: +44 7442 684963 Immediately for your areas of Hacking services I have to share the Good news with everyone so u can be able to know the truth of your spouse through mobile spy or phone spy and the offer other services related hacking and funds recovery. Contact him WhatsApp: +44 ( 7442 684963 ) for any type of hacking, he is a professional hacker that Email: [email protected]
How Wizard George Recovered My Stolen Cryptocurrency
My name is Emily Parker, I work as a special investigator in cybercrime. Earlier this year, I suffered a significant personal loss when my Bitcoin wallet valued at $860,089 was hacked in a sophisticated cyberattack. Despite my experience in investigations, the complexity of cryptocurrency theft made the case extremely challenging. I turned to Wizard George Cyber Service, a firm specializing in digital asset recovery. Their team conducted a thorough blockchain forensic investigation, tracked the stolen funds through multiple transactions and wallets, and successfully recovered my entire Bitcoin amount. I was impressed by their professionalism, technical expertise, and commitment to delivering results. For anyone who has lost cryptocurrency to hacking or fraud, I strongly recommend Wizard George Cyber Service as a trusted and effective solution.
Contact:
🌐 Website: https://wizardgeorgecyberservice.com
📧 Email: wizardgeorgecyberservice(AT) g m a l L. C o M
📞 Phone +1 (807) 698-9213
My crypto wallet was hacked, and I lost $87,000 in BTC and $115,000 in ETH at the time of the breach. I was absolutely devastated, left in shock. In my search for a way to recover my funds, I suspected the breach had happened through my email linked to the wallet, but I couldn’t find any way to regain access, no matter what I tried. I reached out to everyone I trusted, but nothing worked. That was until an old colleague told me about Morphohack Cyber Service, a company specializing in crypto and funds recovery. Without hesitation, I contacted them, and I’m so glad I did. The Morphohack team was incredibly professional and effective, they not only helped me recover my crypto assets but also secured my wallet to prevent future breaches. If you ever find yourself in a similar situation, don’t hesitate to contact Morphohack directly via E-Mail at Morphohack@ cyberservices.com.
C on-tact our service.
Kalfjohnson424 @gmail com
Our List of Service.
▶️Social Media Hack
▶️Phone Hacking
▶️Scammed Crypto Recovery
➡️Increase C re-dit Sc-ore
➡️Website Hacking
➡️University Results Upgrade
➡️Blank ATM Card
➡️Data Recovery
➡️Private Key Reset.
For quick response.
Em -ail: kalfjohnson424 @gmail com
Border us with your jobs & allow us give you positive result with our hacking skills.
(c) 2025 All Right Reserved
Life sometimes can be very disappointing especially when you find out about your spouse’s infidelity. I got in touch with a private expert remotespywise @ gm ail c o m who helped me access my husband’s device after I noticed he always hides things from me. He was super responsive and transparent in his services, don’t wait around and text him right away.
RECOVER YOUR LOST CRYPTO ASSETS WITH ASORE HACK INTELLIGENCE. NO UPFRONT PAYMENT REQUIRED.
Asore Corporation is a team of Cyber Intelligence, Crypto Investigation, Asset Tracing and Offshore Legal experts. Working together to form a boutique cyber and crypto intelligence group focused on providing results.
Using the latest Cyber Tools, Open Source Intelligence (OSINT), Human Intelligence (HUMINT), and cutting edge technology, we provide actionable intelligence to our clients.
WHY CHOOSE US?
– Expert Cyber Investigation Services —Our cyber investigators are certified in the US, UK and experienced with investigations spanning 6 continents.
– Cryptocurrency And Digital Asset Tracking — We are able to track the movement of different crypto currencies and assets. If the cryptocurrency has been moved, we are able to follow it.
– Strategic Intelligence For Asset Recovery — The first step to recovery is locating recoverable assets. Our experienced team will be able to walk you through the process.
Schedule a mail session with our team of professionals today via – asorehackcorp (@) gmail (.) com to get started immediately.
BEWARE of FABRICATED reviews and testimonies endorsing tricksters, do not get scammed twice.
Disclaimer: Asore Corporation is not a law enforcement agency and not a law firm. Like all investigators, we cannot guarantee specific results, but we apply our expertise and resources to every case professionally and ethically….
I discovered Coinfirm on the Coingeco exchanges directory. I want a system that enables me to determine whether my exchange is secure. There solution diligence revealed that the exchange i was using posed a very high risk, thus I am now using a significantly safer exchange. But when it comes to recovery of lost crypto assets, I utilize recoveryhacker101@gmailcom.
Finally i am so happy i found this honest, recommended and reliable hacker before now I have been ripped off by fakes who claimed to be professional hackers until i came by hackerspytech @ gmail com a legit hacker across the internet who helped spy on my fiance phone to save my dying relationship exposing chat evidences on my spouse cheating with friend. being ripped off. I appreciate the good hack services hackerspytech provides, does all sorts of cyber hacks like phone spy monitoring calls, sms, Whatsapp, Viber, Instagram, Kik, Hangout, Snapchat, Facebook it will be done fast honest and reliable i promise will provide result always and won’t expose your confidential data to anyone. The only Ethical hacker i guarantee to talk about employ instead of being victims the expertise as world class, also helped recover all the funds i was ripped off.
Good news — I got back 160,870 of my BITCOIN that was stolen in an investment scam! 🙌 Huge thanks to Brunoe Quick Hack, and the team who worked with me and law enforcement to trace and recover the funds. Whats-APP +(1) 70578-42635
If you ever face something similar: don’t panic, keep every message and transaction record, and get help from verified pros — scams can be beaten when you act fast and use the right channels. Email: BrunoeQuickHackATgmail.com
Marriage is sweet, Love is also sweet but i don’t see why after getting married to my dream man he still cheated on me with his EX girlfriend though i had try breaking into his IPHONE since last year but still not getting access to his phone since then i just try to swallow all my husband had been doing but i can’t take it any more so i came in contact to gmail of jbeespyhack @gmail com, with his help I had access to my husband’s phone without touching his phone. I had full information of his chats with his ex-girlfriend last year. With all I saw, I don’t think I can move on with the marriage. He went as far as telling the girlfriend that I have been his wrong & i beat her up almost everyday. I was so disappointed & I called off the marriage.. and jbeespyhack@gmail com and you can text him your request
HOW TO HIRE A HACKER TO RECOVER STOLEN BITCOIN..
Dune Nectar Web Expert assists individuals and organisations in promptly and compassionately recovering misplaced or misappropriated funds. Our team comprises experienced specialists in financial recovery, fraud investigation, and client advocacy, with strong customer ratings on Google Reviews and Trustpilot. Each case is handled urgently, empathetically, and results-oriented.
Email: “Support (@) Dunenectaronlineexpert . Com”
W/A: https://wa.link/3gfxoy
i don’t like recommending a service , but this hacker really saved me and i think i owe that to them. Are you curious? and you want to penetrate into your spouse, child or any device/ worry no more. contact hackerspyech @ gmail com they can hack and penetrate any device , social media account, delete content from the internet and so more remotely without any trace. i’m so grateful to them , they help save me from a toxic relationship
TRACE AND RECOVER STOLEN BITCOIN/USDT/ETHEREUM CRYPTO INVESTMENT: THROUGH THE SEFTYHUB I am sure. Not everyone has heard about THE SEFTYHUB RECOVERY EXPERT. I recently lost over 870,000 in this cryptocurrency scam after being assured that I would receive a substantial return on my investment within a few days. All of this happened so quickly that I was in shock. My husband almost left me and I was going to lose everything until I came across HUB EXPERT online who are experts in recovering cryptocurrency funds from these scammers. Less a day of consultation, they were able to retrieve all of my money. I’m very grateful to these guys for saving me from becoming a victim. If you have ever fallen victim to a bitcoin or cryptocurrency fraud, I strongly suggest using THE SEFTYHUB to assist you get your money back. EMAIL
SEFTYHUB @GMAIL. COM
TELEGRAM @SEFTYHUB
I was able to spy and monitor my cheating spouse day to day activities with my phone without have a direct access to her target phone and without her knowing…it really surprise me because i never believe such could happen when i was looking for help during my divorce i met a lady who talk about how this great man helped her out of infidelity on Quora, then i contacted them and explain my problem to him and he asked me to drop little information about my spouse infarct, it was like a magic guys under 2 hours i submitted the details he provided me all the information i needed which really helped me during my divorce and i have promise him to share this great opportunity and privileged to people out there especially to those people who might be facing a lot of tremendous challenges on infidelity and needed same help… check him out SEFTYHUB @ gmail . com
I’ve had this monitoring service for 3weeks now, and it definitely serves its purpose as one of my tools for effective employee monitoring in my business. It allowed me to keep track of the messages and files that were sent and received on our company’s devices. It actually increased productivity because the installation of a monitoring software from seftyhub team encouraged our employees to focus on work during work hours… If you need to track and target messages, calls, location, history and all social media seftyhub team are perfect for your job send messages to any of thier contacts DETAILS BELOW
EMAIL👇📧
SEFTYHUB@GMAIL COM
Urgent: Funds Recovered – Claim Your Stolen Bitcoin Now In the fast moving world of cryptocurrency, opportunity and risk often go hand in hand. As digital assets become more mainstream, so do the threats hacks, scams, phishing attacks, and lost wallets. For individuals and businesses navigating this landscape, having a trusted ally can make all the difference. That’s where Intelligence Cyber Wizard steps in. Who They Are Intelligence Cyber Wizard is a specialized cybersecurity and crypto recovery service focused on helping victims of digital asset loss regain control of their funds. Whether it’s a compromised wallet, fraudulent investment scheme, or unauthorized transaction, their mission is clear: restore what was lost and secure what remains. What They Do Their services revolve around three key pillars: 1. Crypto Recovery Expertise Using advanced blockchain tracing techniques, Intelligence Cyber Wizard follows the trail of stolen or misplaced funds across wallets and exchanges. Their team analyzes transaction histories and works to identify points where recovery may be possible. 2. Cybersecurity Protection Recovery is only half the battle. They also help clients strengthen their digital defenses, securing wallets, identifying vulnerabilities, and preventing future attacks. 3. Fraud Investigation & Support From phishing scams to fake investment platforms, they assist clients in understanding how the breach occurred and provide guidance on next steps, including documentation that may be useful for legal or exchange-based recovery efforts. Why It Matters Crypto transactions are decentralized and often irreversible. Unlike traditional banking, there’s no “undo” button. That’s why having a knowledgeable recovery partner is crucial. Intelligence Cyber Wizard bridges the gap between blockchain complexity and real world solutions, offering clarity in situations that can feel overwhelming. A Partner You Can Trust Trust is essential in the crypto space, especially when dealing with recovery services. Intelligence Cyber Wizard emphasizes transparency, confidentiality, and ethical practices. Their approach is rooted in empowering clients not just recovering assets, but educating them to stay protected moving forward. Final Thoughts As the digital economy grows, so will the sophistication of cyber threats. Whether you’re an experienced investor or new to crypto, safeguarding your assets should always be a priority. Intelligence Cyber Wizard positions itself as more than just a recovery service; it’s a long term partner in digital safety. If you ever find yourself facing a crypto related issue, having the right expertise on your side can turn a crisis into a manageable challenge. Email::
SEFTYHUB @GMAIL COM
TELEGRAM @SEFTYHUB
Many people face issues such as online fraud, account compromise, or digital harassment. Instead of trying unsafe solutions, it’s better to contact reputable cybersecurity experts who specialize in legal digital investigations and online safety. They can assist with evidence recovery, account protection, and reporting fraudulent activity
SEFTYHUB @GMAILCOM
Good Day Everyone, My Name Is Margaret Walker, I’m from the USA/Texas. I’m here to share some good news as the world of finance continues to evolve with the growth of cryptocurrencies. After falling victim to a cryptocurrency scam, I lost $354,000 worth of USDT. I was devastated and believed there was no way to recover my hard-earned money. It truly felt like all hope was lost. While searching for help to recover my stolen funds, I came across several testimonials about TOP RECOVERY EXPERT, a recovery specialist who assists victims in retrieving lost cryptocurrency. I decided to contact them, and in less than 24 hours, my Bitcoin was fully recovered. I am extremely grateful for their assistance. Their security team was professional, kept me updated throughout the entire process, and demonstrated a deep understanding of blockchain transactions and recovery protocols. They proved to be reliable and trustworthy. Thanks to TOP RECOVERY EXPERT for being there and providing the support you needed help, contact Call/Text:+1 (346) 980-9102 OR Email: [email protected]
Looking for a way out? It’s simple, When it comes to tracking Locations of mobile phones, computer system & individuals using them or remote mobile hacking into devices, This Genius hacker provides the very best of services, I’m glad to introduce him to you all, I have been fooled many times by some other Sham hackers that pretend to be what they are not and it really makes me feel bad. I was at the point of giving up, but luckily, I was introduced to the best hacker ever, contact his gmail on jbeespyhack@ gmail com who he eventually offered me the best solution I ever needed retrieving some old deleted texts and a round-the-clock location monitoring of my husband’s phone and everything worked fine, he’s very fast honest and reliable, work with him today for the best solution. contact him on jbeespyhack@ gmail com